Dark Reading reports that the average data breach costs businesses around $4.5 million per incident, something that many companies find impossible to recover from.
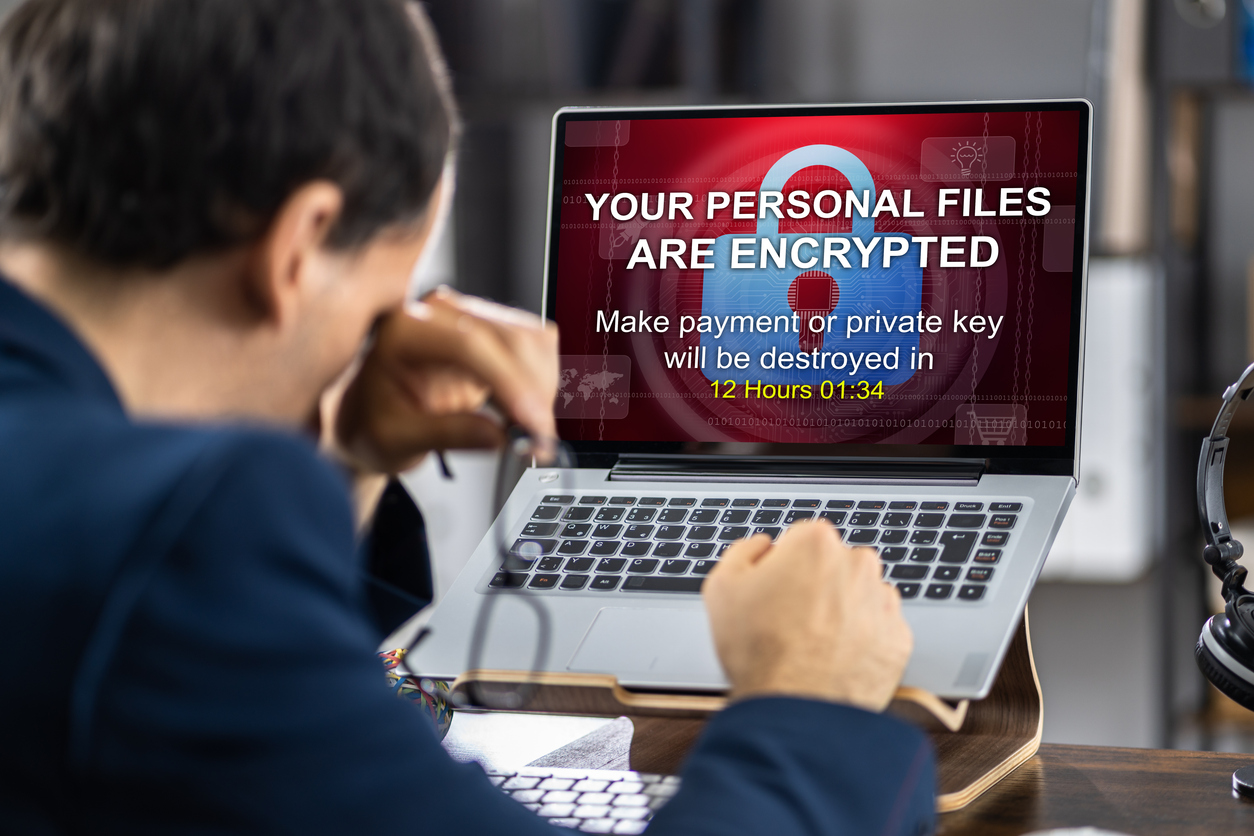
When a cyberattack locks down your files, time becomes your greatest enemy. Businesses that aren’t prepared often lose more than data.
They lose trust, money, and control. That’s why ransomware recovery isn’t something to figure out after the damage is done. It needs to be part of your planning from the start.
Risks Businesses Face After an Attack
One ransomware event can ripple through every part of your operations. Financial losses are only part of the damage. Trust and client relationships often suffer in ways that take years to repair.
Employees may struggle to carry out daily tasks, and entire systems can remain paralyzed without access. These situations show how crucial ransomware protection becomes before problems arise.
Why Timing Matters During a Breach
The first minutes after a breach can determine how much damage occurred. Delays in response often lead to deeper encryption and greater data loss. Quick action keeps the attacker from moving laterally through systems and limits long-term harm.
Having a reliable cyberattack response plan lets your team follow clear steps without hesitation. It also ensures that no one wastes time guessing what to do next.
How to Handle Communication and Containment
Leaders must decide what to share and when, both inside and outside the company. Missteps in communication can cause panic or confusion, making the situation worse.
Teams should isolate affected systems and begin malware removal to stop the spread. You also need to coordinate with law enforcement and possibly third-party experts.
Restoring Access Without Losing Critical Data
Once systems are isolated, focus shifts to bringing everything back online safely. A solid system of backups can mean the difference between a quick fix and total loss.
Even then, poor planning can result in overwritten or missing files. Smart businesses build data recovery strategies that protect their most vital information.
Restoring operations without rushing helps maintain accuracy and stability. Some steps help ensure a smoother recovery process:
- Verify the integrity of backups before use
- Restore systems in order of operational priority
- Keep clean copies of core applications off-network
- Monitor recovered systems for hidden threats
These steps help avoid setbacks and reduce the risk of reinfection during recovery.
Steps to Prevent Future Intrusions
Once recovery is complete, the focus must shift to long-term defense. Many companies repeat the same mistakes because they don’t review what failed.
A strong framework for ransomware recovery includes regular testing and updates to protocols. Adding stronger system backup solutions helps build layers of protection.
Develop a Comprehensive Ransomware Recovery Strategy
No company can eliminate every risk, but a clear ransomware recovery plan gives you the upper hand when it matters most. Understand the warning signs, prepare your defenses, and act quickly when systems are compromised.
Pegasus Technologies provides managed IT services tailored to your business and your team’s personality. With offices in Kennett Square, Media, and Wayne, PA, we offer expert support without the cost of a full-time IT department.
Our hand-picked technicians build personal connections that make your technology more reliable, secure, and efficient. You can get in touch with us today to learn more about how we can help.